We have a Zabbix v1.8.X (with MySQL) server hosted on a Debian Squeeze VM. This VM is being migrated to Debian Wheezy, and therefore requires Zabbix to be moved as well.
However, due to security related issues Zabbix packages were removed from Wheezy.
So, what we are going to do is to install Zabbix 1.8.19 from source, and restore the database backup we have created on a Squeeze VM.
The plan is as below:
- Install pre-required software.
- Restore Zabbix 1.8 database from a backup.
- Download, configure and compile Zabbix 1.8.19 source code.
- Create directories, copy and modify configuration files.
- Install Apache and PHP for Zabbix web interface.
- Generate and install a self-signed SSL certificate for secure HTTPS browsing.
- Configure Apache and PHP settings.
Install Pre-required Software
Update package list:
# apt-get update
C compiler, make, libcurl and snmp libraries:
# apt-get install wget gcc make libcurl4-gnutls-dev libsnmp-dev libnet-snmp-perl
MySQL database and its libraries:
# apt-get install mysql-server libmysqld-dev libmysqlclient-dev
Create Zabbix MySQL User and Restore Zabbix Database From a Backup
Login to MySQL server as root and create a new zabbix database. Create a new MySQL user for zabbix called “zbuser” and grant all privileges on zabbix database.
# mysql -uroot -p mysql> CREATE DATABASE zabbix; mysql> GRANT ALL PRIVILEGES ON zabbix.* TO "zbuser"@"localhost" IDENTIFIED BY "zbpass"; mysql> FLUSH PRIVILEGES; mysql> SHOW grants FOR 'zbuser'@'localhost'; +------------------------------------------------------------------------------+ | Grants for zbuser@localhost | +------------------------------------------------------------------------------+ | GRANT USAGE ON *.* TO 'zbuser'@'localhost' IDENTIFIED BY PASSWORD '*1[...]A' | | GRANT ALL PRIVILEGES ON `zabbix`.* TO 'zbuser'@'localhost' | +------------------------------------------------------------------------------+ 2 rows in set (0.03 sec) mysql> quit;
Restore the database from a backup file:
# mysql -uzbuser -p zabbix < zabbix_backup.sql
Configure and Compile the Source Code
Download the source code:
# cd ~ # wget http://netcologne.dl.sourceforge.net/project/zabbix/ZABBIX%20Latest%20Stable/1.8.19/zabbix-1.8.19.tar.gz
Extract the archive file:
# tar xvfz zabbix-1.8.19.tar.gz
Change into extracted directory and configure:
# cd zabbix-1.8.19 # ./configure --enable-server --enable-agent --with-mysql --with-net-snmp \ --with-libcurl --with-ldap --enable-ipv6
Make and install everything:
# make install
Create and Modify Configuration Files and Directories
Create zabbix user:
# useradd -d /var/run/zabbix -s /bin/false zabbix
Create a folder to store configuration files:
# mkdir /etc/zabbix
Also create a folder to keep pid files:
# mkdir /var/run/zabbix # chown zabbix:zabbix /var/run/zabbix
Checking where we are:
# pwd /root/zabbix-1.8.19
Copy default configuration templates for server and agent:
# cp ./misc/conf/zabbix_agentd.conf /etc/zabbix/ # cp ./misc/conf/zabbix_server.conf /etc/zabbix/
Remove world permissions as the server config file will contain MySQL password:
# chmod 0750 /etc/zabbix/zabbix_server.conf
Create directories to keep logs:
# mkdir /var/log/zabbix-agent /var/log/zabbix-server # chown zabbix:zabbix /var/log/zabbix-agent /var/log/zabbix-server
Server configuration file should look as below:
# cat /etc/zabbix/zabbix_server.conf ListenPort=10051 ListenIP=0.0.0.0 LogFile=/var/log/zabbix-server/zabbix_server.log DebugLevel=2 PidFile=/var/run/zabbix/zabbix_server.pid DBHost=localhost DBName=zabbix DBUser=zbuser DBPassword=zbpass DBPort=3306 HousekeepingFrequency=24 DisableHousekeeping=0 Timeout=3
Agent configuration file should look as below:
# cat /etc/zabbix/zabbix_agent.conf ListenPort=10050 ListenIP=0.0.0.0 PidFile=/var/run/zabbix/zabbix_agentd.pid LogFile=/var/log/zabbix-agent/zabbix_agentd.log LogFileSize=0 Server=127.0.0.1,localhost
Copy init scripts:
# cp ./misc/init.d/debian/zabbix-server /etc/init.d/ # cp ./misc/init.d/debian/zabbix-agent /etc/init.d/
Change the default PID file for server. Open /etc/init.d/zabbix-server and make changes as below:
#PID=/tmp/$NAME.pid
PID=/var/run/zabbix/$NAME.pid
DIR=/var/run/zabbix
# add this to ensure the folder is created
if [ ! -d "$DIR" ]; then
mkdir /var/run/zabbix
chown zabbix:zabbix /var/run/zabbix
fi
Now change the default PID file for agent. Open /etc/init.d/zabbix-agent and make changes as below:
#PID=/tmp/$NAME.pid
PID=/var/run/zabbix/$NAME.pid
DIR=/var/run/zabbix
# add this to ensure the folder is created
if [ ! -d "$DIR" ]; then
mkdir /var/run/zabbix
chown zabbix:zabbix /var/run/zabbix
fi
Start Zabbix Server and Agent
Start server daemon:
# service zabbix-server start Starting Zabbix server daemon: zabbix_server
Start agent daemon:
# service zabbix-agent start Starting Zabbix agent daemon: zabbix_agentd
Check that both daemons are running:
# netstat -nltp | grep zabbix tcp 0 0 0.0.0.0:10050 0.0.0.0:* LISTEN 31813/zabbix_agentd tcp 0 0 0.0.0.0:10051 0.0.0.0:* LISTEN 31760/zabbix_server
Install Zabbix WEB Interface
We’ll need a php capable webserver for this:
# apt-get install apache2 php5 libapache2-mod-php5 php5-mysql php5-gd openssl ssl-cert
Get rid of annoying “could not reliably determine the server’s fully qualified domain name” warning:
# echo "ServerName localhost" >> /etc/apache2/apache2.conf
Create a subdirectory for Zabbix virtual host:
# mkdir /var/www/zabbix
Copy php frontend files:
# cd /root/zabbix-1.8.19/frontends/php # cp -a ./ /var/www/zabbix
Change permissions:
# chown -R root:root /var/www/zabbix
Generate and Install a Self-Signed SSL Certificate
We want to push everything through a secure TLS/SSL connection.
# mkdir /etc/ssl/webserver && cd /etc/ssl/webserver
Generate a self-signed certificate:
# openssl req -new -x509 -days 1825 -sha256 -nodes -out ./server.crt \ -keyout ./server.key
Make the private key readable by the root user only:
# chmod 0600 ./server.key
Configure Apache to Use the Certificate
Open /etc/apache2/sites-available/default-ssl and change the lines below:
SSLCertificateFile /etc/ssl/certs/ssl-cert-snakeoil.pem SSLCertificateKeyFile /etc/ssl/private/ssl-cert-snakeoil.key
to the following:
SSLCertificateFile /etc/ssl/webserver/server.crt SSLCertificateKeyFile /etc/ssl/webserver/server.key
Enable Apache TLS/SSL Support
When we talk about SSL, we actually refer to TLS. SSL is an older version of cryptographic protocols for encrypting data across the internet.
# a2enmod ssl # a2ensite default-ssl # service apache2 restart
Enable Apache Rewrite Module
We’ll force all requests coming to a standard HTTP port 80 to be forwarded to a secure HTTPS 443 port:
# a2enmod rewrite
Open:
# vim /etc/apache2/sites-available/default
And add the following lines in red:
<VirtualHost *:80> ServerAdmin [email protected] RewriteEngine On RewriteCond %{HTTPS} off RewriteRule (.*) https://%{HTTP_HOST}%{REQUEST_URI} [...]
Restart Apache:
# service apache2 restart
Some Information Disclosure Related Apache Tuning
Hide apache version and signature from being shown online. Open /etc/apache2/conf.d/security and change the following parameters:
ServerSignature off ServerTokens prod
Reload apache to pick up configuration changes:
# service apache2 reload
Configure PHP Settings
Create non world-writeable directories for temporary HTTP uploaded files as well as php session:
# mkdir -p -m 0750 /var/www/php_dir/temp # mkdir -p -m 0750 /var/www/php_dir/session # chown -R www-data:www-data /var/www/php_dir
Open /etc/php5/apache2/php.ini and modify the following settings as per below:
open_basedir = Off expose_php = Off max_execution_time = 600 max_input_time = 600 memory_limit = 256M display_errors = Off display_startup_errors = Off register_globals = Off post_max_size = 32M magic_quotes_gpc = Off upload_tmp_dir = "/var/www/php_dir/temp" upload_max_filesize = 16M max_file_uploads = 5 allow_url_fopen = Off allow_url_include = Off date.timezone = "Europe/London" session.save_path = "/var/www/php_dir/session"
# service apache2 reload
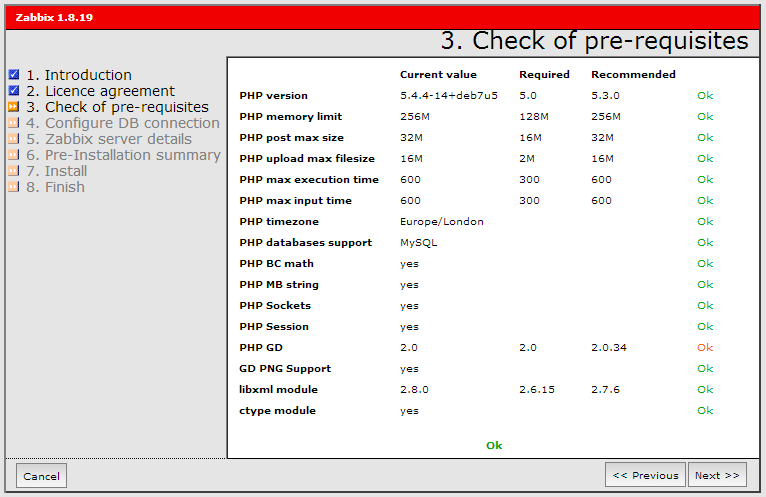
Now we need to point a web browser to https://localhost/zabbix and finish the installation. Checklist should look as below:
We will need to copy the zabbix.conf.php file to the /var/www/zabbix/conf/ directory as the webserver does not have write access to it. Once finished the installation, we can log in by using an existing web account.
Configure Iptables
# iptables -A INPUT -p tcp -m multiport --dport 80,443,10051 -j ACCEPT

Hi Tomas. I found your post very usefull so I’d like to start with a huge TANK YOU! I’m new to Zabbix and I’d like to replace self-signed cert for one of my own as we host our own internal Enterprise CA/PKI infrastructure. Would you please guide me in the steps to perform for this? Once again, thank you so much.
Hi Fernando, thanks, I’m glad you found this post useful.
As for replacing a self-signed certificate, it depends on where your current certificates are stored. In simple words, just replace old certificates with new ones using the same naming, reload all relevant services which use those certificates and you are all set.