Setting up an OpenVPN server on a Windows Server 2008 hosted on AWS. Also tested on Windows Server 2012 R2.
Install OpenVPN
Download the package from the official website here (OpenVPN 2.3.2) and install OpenVPN server on a Windows machine. Make sure that you install the OpenSSL utilities and OpenVPN RSA certificate management scripts.
[UPDATE: July 2014] Note that easy-rsa was included with 2.3.2, but is no longer bundled with OpenVPN source code archives (according to the OpenVPN downloads page). To get it, visit the easy-rsa page on GitHub.
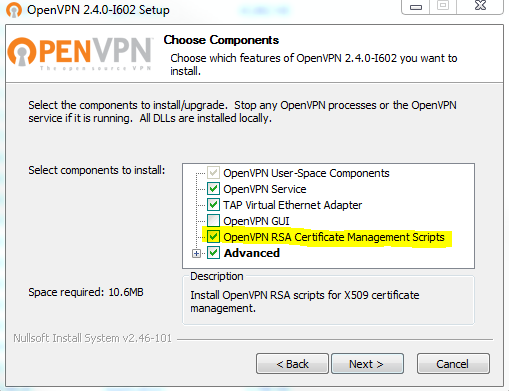
[UPDATE: February 2016] Instructions have been tested with OpenVPN 2.4.0 on Windows Server 2012 R2. When you install OpenVPN, make sure the following box is ticked:
We have Windows Firewall disabled. We are going to need to open a UDP port 11194 in the AWS security group associated with the server.
Optional: Rename TAP-Windows Adapter V9
Find which network interface that is not connected to the Internet and has the device name listed as “TAP-Windows Adapter V9”. Rename the TAP adapter to “tap-vpn” for the sake of clarification.
Generate the Master Certificate Authority (CA) Certificate and Key
Open up a Command Prompt windows as Administrator and change directory to C:\Program Files\OpenVPN\easy-rsa:
C:\Users\Administrator> cd \Program Files\OpenVPN\easy-rsa
Run the following batch file to copy configuration files into place:
> init-config
Now edit the vars file (it’s called vars.bat on Windows):
> notepad vars.bat
And set the parameters below appropriately:
KEY_COUNTRY=GB KEY_PROVINCE=Midlands KEY_CITY=Birmingham KEY_ORG=Private [email protected] KEY_CN=changeme KEY_NAME=changeme KEY_OU=IT
Don’t leave any of these parameters blank. Next thing to do is to initialise the PKI:
> vars > clean-all > build-ca
Generate a Certificate and a Private Key for the Server
> build-key-server server
Generate a Certificate and a Private Key for the Client
Generating client certificates is very similar to the previous step. Make sure that the Common Name value matches the server’s value and the Name value is specified. We can leave all other settings default.
> vars > build-key client
Generate a Diffie Hellman Parameter for the OpenVPN Server
> build-dh
Creating Configuration Files for a Server and Clients
Copy the template file C:\Program Files\OpenVPN\sample-config\server.ovpn to C:\Program Files\OpenVPN\config:
> copy ..\sample-config\server.ovpn ..\config
1 file(s) copied.
Modify Configuration File For Server
Open the configuration file server.ovpn for editing:
> notepad ..\config\server.ovpn
Make it look as below:
#listen on IPv4 local 0.0.0.0 #the default port is 1194 #we use a non-default port 11194 port 11194 #UDP protocol chosen for better protection against DoS attacks and port scanning proto udp #using routed IP tunnel dev tun #relative paths to keys and certificates ca ..//easy-rsa//keys//ca.crt cert ..//easy-rsa//keys//server.crt key ..//easy-rsa//keys//server.key dh ..//easy-rsa//keys//dh1024.pem #set OpenVPN subnet server 10.26.0.0 255.255.255.0 #maintain a record of client-to-virtual-IP-address ifconfig-pool-persist ipp.txt #ping every 10 seconds, assume that remote peer is down if no ping received during 60 keepalive 10 60 #cryptographic cipher, must be the same (copied) on the client config file as well cipher AES-256-CBC #enable compression on VPN link comp-lzo max-clients 20 #try to preserve some state across restarts persist-key persist-tun #log file status ..//log//openvpn-status.log #log file verbosity verb 3
We don’t need to make any other changes.
Start OpenVPN Server
Run from a command prompt window:
> openvpn ..\config\server.ovpn
Once running in the command prompt window, OpenVPN can be stopped by the F4 key.
Service also can be controlled from Start Menu -> Administrative Tools -> Services.
Ensure that the OpenVPN server is running:
> netstat -na | findstr /L 11194 UDP 0.0.0.0:11194 *.*
Setup OpenVPN Client
Download the installation package here and install the OpenVPN client software.
We need to copy the template file C:\Program Files\OpenVPN\sample-config\client.ovpn from the server to our client PC’s folder C:\Program Files\OpenVPN.
Also copy ca.crt, client.crt and client.key from C:\Program Files\OpenVPN\easy-rsa\keys to our client PC’s folder C:\Program Files\OpenVPN\config.
Modify Client Configuration File
Open the configuration file client.ovpn for editing, and make it look like this:
client
dev tun
proto udp
remote openvpn.example.com 11194
resolv-retry infinite
nobind
persist-key
persist-tun
ca ca.crt
cert client.crt
key client.key
ns-cert-type server
cipher AES-256-CBC
comp-lzo
verb 3
Connect to OpenVPN server
Launch the OpenVNP client, click “Connection Profiles” -> “Local File”, find client.ovpn, save the file. Click connect.
Alternatively, run from a command prompt window:
> cd \Program Files\OpenVPN\config > openvpn .\client.ovpn
All done. We should now be able to RDP to the server by using its private IP 10.26.0.X.

I config like you,but when i use openvpn client to internet ,client cannot out to internet , my status local Area Connection(TAP-Windows-Adapter V9) at IPv4 Connectivity:No Internet access
myserver window 7
myclient window7
Thank you very much
I live in Thailand
Is firewall configured to allow VPN traffic? Did you enable IP Forwarding on your server?
Half of the things described here are not up to date. It refers to files that do not exist, and Windows totally don’t know what to do with half of the command line instructions. These are examples of what the elevated command line in Windows returns:
WARNING: can’t open config file: /etc/ssl/openssl.cnf
unknown option -config
Could Not Find C:\*.old
Options error: –dh fails with ‘dh2048.pem’: No such file or directory
Options error: –ca fails with ‘ca.crt’: No such file or directory
Options error: –cert fails with ‘server.crt’: No such file or directory
Options error: –key fails with ‘server.key’: No such file or directory
Options error: Please correct these errors.
FINDSTR: Cannot open UDP
FINDSTR: Cannot open 0.0.0.0:11194
Those are a lot of errors. Can this guide be replaced by an up to date explanation for OpenVPN version 2.3.8? The current guide is not working anymore. Any help would be appreciated.
This article was written year and a half ago, it is expected that things get outdated as the time passes by.
What version of Windows are you using? What version of OpenSSL? What version of OpenVPN? Which command in particular gives the error?
Updating the article would require my time and resources. Are you willing to pay for any? :)
…and the contents of server.ovpn of the 2.3.8 version are much different than described on this page. I don’t know where to put those information on which lines, because of the different version this page is speaking about.
Have you checked the official documentation? There are quite a few Windows notes published that you may find useful.
I didn’t use OpenVPN 2.3.8 myself and therefore cannot really help much at this time.
Thanks for the post, I used this instruction – http://sysadm.pp.ua/linux/shifrovanie/openvpn-client-server.html . Can anybody suggest some usefull mobile OpenVPN client?
Your instruction are for a Linux server, this post is for a Windows machine. If you need instructions for a Linux box, check this page: https://www.lisenet.com/2013/openvpn-server-setup-on-linux/
OpenVPN client is available for Android, have you tried it? I use it on a daily basis.
I got a message: “VERIFY ERROR: depth=1, error=self signed certificate in certificate …”. What do I have to do to fix this?
It looks like a problem with your CA certificates. Make sure you have them on the client machine.
Hi Tomas,
I think its a good job, first of all… anybody know that time passes by… and have to be up to date. ;)
Just some questions:
* Have you opened 11194 UDP port in your router to your local Ethernet private IP?
* Have you configure anything in TAP nic?
* Have you configure static routes somewhere?
Im trying to set up at home and i cant “RDP-ing” my PC (OVPN server is on it – Ethernet nic and TAP nic) so i connect client to server but can not RDP my PC.
Thks in advance
I agree with you in terms of being up to date, however, I no longer use Windows :)
I wrote a message a few hours ago and now is not here, what happens?
thks
All messages get manually approved before they appear on the comments board.
I’ve tried and make it exactly like Tomas on the local network, and it works well. For openvpn server must be connected first in the OpenVPN GUI in order to tap adapter can accept connections from the outside, then the client can connect to the server.
* For the server I’m using Windows XP 32-bit and openvpn Installer (32-bit), Windows XP swupdate.openvpn.org/community/releases/openvpn-install-2.3.11-I001-i686.exe
* Openssl in the server slproweb.com/download/Win32OpenSSL_Light-1_0_2h.exe
* Replace port 1194 in server.ovpn
– For the client I use windows 7 64-bit and Installer (64-bit), Windows Vista and later swupdate.openvpn.org/community/releases/openvpn-install-2.3.11-I601-x86_64.exe.
– Replace “remote xxx.xxx.xxx.xxx” 1194 in client.ovpn
note: ip xxx.xxx.xxx.xxx replaced with a computer that was made into a server
And it works well.
Currently I am just trying to the local network, not using the internet network. Supposedly by setting like this, it can be done for vpn over the internet, as long as the modem router has been made for the forward port 1194 to a computer that is in use as a server.
thank you Tomas, very nice
Welcome.
Hi,
With the last package Openvpn, since version 2.3 , Easy-rsa 3 is not with and we have to see here : https://github.com/OpenVPN/easy-rsa
But the download for Windows is not complete and we have not all .bat files like with the old easy-rsa
On github, the search for the good files modified, v 3.0.1 or v 3.0.2 are difficult.
May be, you have the good information and procedures to create on Windows the differents certificates.
Have a good day.
It so happened that a few day ago I had to deploy an OpenVPN server on Windows 2012 R2.
I installed OpenVPN 2.4.0 by following this very blog post, and had no issues at all.
Thanks a lot, worked like a charm!
You’re welcome.
tls-auth ta.key
i do too
Hello. Is your tutorial still current? Indeed, I would like to install openvpn server on windows server 2016/ 2019 and use a windows or android client.
If so, how to do it because even if it seems that the connection is made, I no longer have access to internet.
And how to access my local network (smb) and access the rdp
Sorry for my english, i had to use a translator
Thank you
Hi Paul, the tutorial should still work in general unless something major has changed with OpenVPN configuration. Having said that, I’ve not tried OpenVPN with Windows Server 2016/2019 therefore some tweaks may be required.
Can you run a packet trace on your OpenVPN server to see where packets are being routed to/dropped?
Hi Lisenet,
Thanks for the tutorial it sure works fine; i mean the whole settings part, the only problem here is the port, still remains closed.
Any suggestions??
Is the service listening on the port? You can use netstat to check it. Also, did you open the port on the firewall?
Hello
Thanks for the walkthrough. The resulting client file throws this log:
2021-11-26 10:53:51 OpenSSL: error:140AB18E:SSL routines:SSL_CTX_use_certificate:ca md too weak
2021-11-26 10:53:51 MANAGEMENT: Client disconnected
2021-11-26 10:53:51 Cannot load certificate file C://Program Files//OpenVPN//config//client.crt
2021-11-26 10:53:51 Exiting due to fatal error
I’m using Windows server 2012 and the Latest OpenVPN version.
Any help would be appreciated.
The log message says that the certificate file cannot be loaded. Does the file exist?
Sun Apr 17 10:25:49 2022 OpenSSL: error:0906D06C:PEM routines:PEM_read_bio:no start line
Sun Apr 17 10:25:49 2022 OpenSSL: error:140AD009:SSL routines:SSL_CTX_use_certificate_file:PEM lib
Sun Apr 17 10:25:49 2022 MANAGEMENT: Client disconnected
Sun Apr 17 10:25:49 2022 Cannot load certificate file C:\Program Files\OpenVPN\config\client.crt
Sun Apr 17 10:25:49 2022 Exiting due to fatal error
The error suggests that your certificate file cannot be loaded.
hi. everything works well however my connected clients do not have internet connection when connected to the vpn. Any ideas?
Are VPN clients configured to use the VPN server as their default gateway?