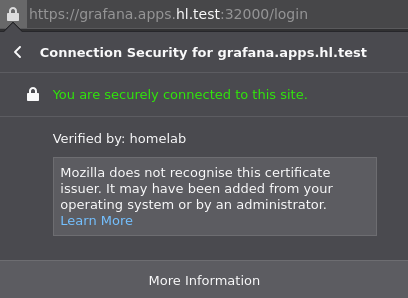
I use my own Root CA to manage certificates in the homelab environment.
Create a Root CA Certificate
Generate a Root CA that is valid for 10 years:
$ openssl req -newkey rsa:2048 -keyout homelab-ca.key -nodes -x509 -days 3650 -out homelab-ca.crt
Verify X509v3 extensions:
$ openssl x509 -text -noout -in homelab-ca.crt | grep CA
CA:TRUE
Import the Root CA in to your browser.
Create a Wildcard Kubernetes Certificate Signed by the Root CA
Generate a private key:
$ DOMAIN="*.apps.hl.test"
$ openssl genrsa -out "${DOMAIN}".key 2048 && chmod 0600 "${DOMAIN}".key
Generate a Certificate Sign Request (CSR):
$ openssl req -new -sha256 -key "${DOMAIN}".key -out "${DOMAIN}".csr
Sign the request with the Root CA:
$ openssl x509 -req -in "${DOMAIN}".csr -CA homelab-ca.crt -CAkey homelab-ca.key -CAcreateserial -out "${DOMAIN}".crt -days 1825 -sha256
When I use this wildcard certificate with Grafana, it appears as trusted.