We will configure LDAP authentication on a CentOS 7 server.
Software
Software used in this article:
- CentOS 7
- nss-pam-ldapd 0.8.13
- nscd 2.17
Installation
The nscd package comes as a dependency for the nss-pam-ldapd and can therefore be omitted.
# yum install -y nss-pam-ldapd nscd
The nss-pam-ldapd package allows LDAP directory servers to be used as a primary source of name service information. The file contains options, one on each line, defining the way NSS lookups and PAM actions are mapped to LDAP lookups.
The file nslcd.conf contains options, one on each line, defining the way NSS lookups and PAM actions are mapped to LDAP lookups.
LDAP Authentication Configuration
SELinux is set to enforcing mode.
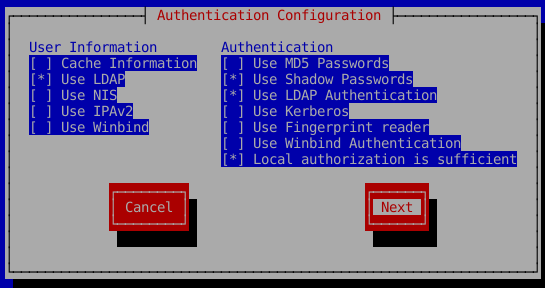
We are going to use an OpenLDAP server which we set up some time ago. Run the authconfig in a text mode. Note that there is a GUI version of the tool available, look for authconfig-gtk.
# authconfig-tui
Our configuration can be seen below.
We use the ldaps protocol and therefore bind to 636 port directly.
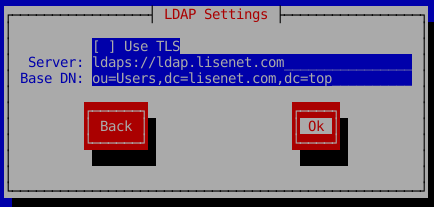
Another option is to use StartTLS (see “Use TLS” above). This, however, requires us to have a plain LDAP port 389 open on the network (which we don’t) as the client needs to establish an unencrypted connection with the directory server first. Also note that to connect to an LDAP server with TLS protocol enabled we need a CA certificate which signed out server’s certificate. It has to be in the PEM format and copied to the directory /etc/openldap/cacerts/.
In a case where a self-signed certificate is used, the following parameter should be set in the file /etc/nslcd.conf to avoid getting “peer’s certificate issuer has been marked as not trusted by the use” error:
tls_reqcert never
Once the configuration is complete, it should all be good really assuming the LDAP server allows anonymous read access. In our case it does not, therefore we have to do one more thing and put some authentication credentials to be able to bind successfully.
Open /etc/nslcd.conf and add the following lines:
# The distinguished name to bind to the server with. # Optional: default is to bind anonymously. binddn cn=guest,dc=top # The credentials to bind with. # Optional: default is no credentials. # Note that if you set a bindpw you should check the permissions of this file. bindpw passwd
Restart the nslcd service:
# systemctl restart nslcd
Try to login with an LDAP user:
# su - ldapuser1 Last login: Sat Mar 19 18:38:42 GMT 2016 on pts/1 su: warning: cannot change directory to /home/ldapuser1: No such file or directory id: cannot find name for group ID 2001 -bash-4.2$
We can ignore warnings.
$ id uid=2001(ldapuser1) gid=2001 groups=2001 context=unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023
These below are purely for future references.
# grep -ve "^$" -ve "^#" /etc/openldap/ldap.conf TLS_CACERTDIR /etc/openldap/cacerts SASL_NOCANON on URI ldaps://ldap.lisenet.com BASE ou=Users,dc=lisenet.com,dc=top
# grep -ve "^$" -ve "^#" /etc/nslcd.conf uid nslcd gid ldap uri ldaps://ldap.lisenet.com base ou=Users,dc=lisenet.com,dc=top binddn cn=guest,dc=top bindpw passwd base group ou=Groups,dc=lisenet.com,dc=top tls_reqcert never ssl no tls_cacertdir /etc/openldap/cacerts
# grep ldap /etc/nsswitch.conf passwd: files sss ldap shadow: files sss ldap group: files sss ldap netgroup: files sss ldap automount: files ldap
Troubleshooting
# journalctl -xlf
Also check LDAP server logs.
A note to myself, when setting up LDAP users, ensure that they have a valid loginShell attribute defined, for example /bin/bash. Otherwise we may hit the following issue:
This account is currently not available.
It will happen when a loginShell attribute is set to /sbin/nologin.

Hi,
I followed this procedure (that I can also found on my website) and it’s very easy… I can open very easily a console (local session on my Linux box) But I have a problem when I would like to open a session via OpenSSH Terminal. The LDAP authentication not work.
Do you known how to tweak OpenSSH to make reference through the NSLCD
I’ve just tried this configuration in my test lab, and it works fine. OpenSSH server configuration must have the following line:
It does not need to have that line , that’s for kerberos auth
If it doesn’t work than you’ve done something wrong , which most of the time has something to do with LDAPS/STARTTSL certificates not being trusted , from my experience.
Hi ,
thank you for this article .it is working with freeipa. when ı used to anonymous bind.
But how can ı do if ı close to anonymous bind from my ldap server? which configuration ı should add user id and passwd ?
Hi Lisenet.
What if we need to provide multiple base dn in nslcd file. For example i was trying to authenticate my client with ou=admin and ou=devops only. I have tried with the below entry but it is not restricting the groups.
base group ou=admin,dc=shakdomain,dc=com
base group ou=devops,dc=shakdomain,dc=com
Hi,
My nslcd.service is getting inactive automatically.
Please suggest how to troubleshoot
Please check nslcd logs, also check the journal for any additional info.
Enable debugging mode, note that nslcd will not put itself in the background but will send verbose debugging info to stderr.
Please check below details:
****************************************************************************************************
EMM002VM002400APP002:/etc# grep -ve “^$” -ve “^#” /etc/openldap/ldap.conf
TLS_CACERTDIR /etc/openldap/certs
SASL_NOCANON on
*************************************************************************************
EMM002VM002400APP002:/etc# grep -ve “^$” -ve “^#” /etc/nslcd.conf
uid nslcd
gid ldap
uri ldaps://ldaps.vodafone.com.au
base DC=VHA,DC=internal
binddn CN=svc_npe_vemm,OU=EricssonSVC,OU=Service Accounts,DC=VHA,DC=internal
bindpw Asrv@vE33
tls_reqcert never
tls_cacertdir /Vodafone/archive/Certificates/LDAP/
nss_initgroups_ignoreusers root,mmsuper,postgres,vmfuser,pmuser,sftpuser,esauser,ut_test
map passwd homeDirectory “/home/$uid”
referrals off
************************************************************************************************
EMM002VM002400APP002:~# grep ldap /etc/nsswitch.conf
passwd: files sss ldap
shadow: files sss ldap
group: files sss ldap
netgroup: nisplus sss ldap
automount: files ldap
***********************************************************************************************
Is this your homelab, or are you setting this up for work?
Hi,
is this guide also recommended for centos 5?
Thanks
No, it isn’t.