We’re going to install Foreman with Katello on CentOS 7.
This article is part of the Homelab Project with KVM, Katello and Puppet series.
Katello vs Spacewalk vs Red Hat Satellite
We have been using Spacewalk for quite some time. Spacewalk is an upstream product for Red Hat Satellite 5. Red Hat Satellite 6 is a re-engineering of the Red Hat Satellite product, it has been built from the ground-up on different and more modern technologies. Red Hat Satellite 6 is a federation of several upstream open source projects, including Katello, Foreman, Pulp and Candlepin. All products are open source projects, and Red Hat is the biggest contributor in each case. What does each product do?
- Foreman: provisioning on new clients.
- Pulp: patch and content (package repository) management.
- Candlepin: subscription and entitlement management.
- Puppet: configuration management (actual running of modules assigned in Foreman).
- Katello: unified workflow and WebUI for content (Pulp) and subscriptions (Candlepin).
Initially Katello was a standalone application, but it’s now a plugin to the Foreman. Foreman is a complete lifecycle management tool for physical and virtual servers. When we talk about Katello, we have in mind a Foreman server with Katello plugin.
Software
Software used in this article:
- CentOS 7
- Foreman 1.16
- Katello 3.5
- Puppetserver 2.8
- Puppet 4.10
Virtual Machine Hardware
The VM that we are going to use for Katello has the following specifications:
- 2 CPU cores
- 10GB RAM + 4GB SSD-backed swap
/– 10GB/var/lib/pulp– 10GB/var/lib/mongodb– 10GB/var/ftp/pub– 10GB/var/spool/squid– 10GB/tmp– 1GB/mnt/backup– 50GB
The XFS file system is recommended for Katello because it does not have the inode limitations that ext4 does. As Katello uses a lot of symbolic links it is likely that our system will run out of inodes if using ext4 and the default number of inodes.
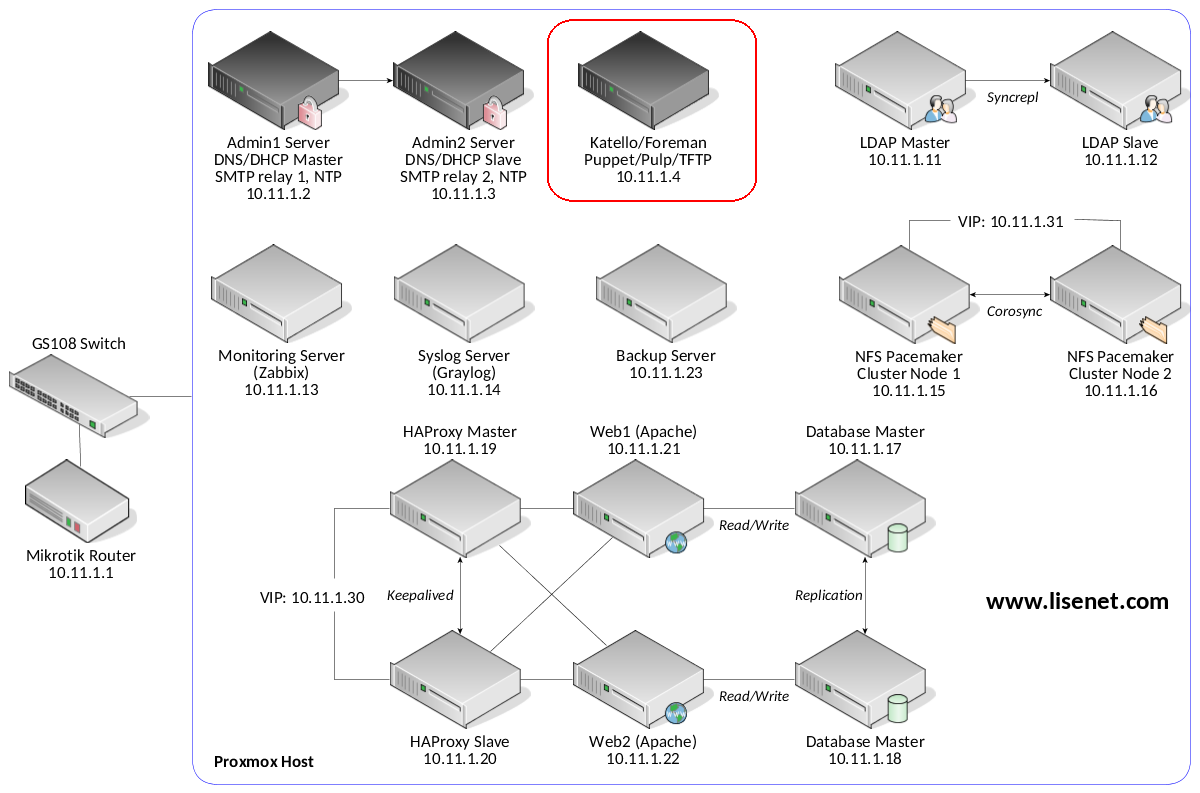
Homelab
See the image below to identify the homelab part this article applies to.
Time Sync
According to Katello documentation provided here https://theforeman.org/plugins/katello/3.5/installation/index.html, several Katello features will not function well if there is minor clock skew. Setup chronyd:
# yum install chrony -y # systemctl enable chronyd && systemctl start chronyd # chronyc sources
DNS is configured to use our homelab servers:
# cat /etc/resolv.conf
nameserver 10.11.1.2
nameserver 10.11.1.3
Install Katello
Configure Firewall
# firewall-cmd --permanent --add-service={RH-Satellite-6,ftp,tftp}
# firewall-cmd --permanent --add-port=8000/tcp
# firewall-cmd --reload
# firewall-cmd --list-all public (active) target: default icmp-block-inversion: no interfaces: enp0s17 sources: services: ssh dhcpv6-client RH-Satellite-6 ftp tftp ports: 8000/tcp protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules:
Add Repositories
# yum -y localinstall http://fedorapeople.org/groups/katello/releases/yum/3.5/katello/el7/x86_64/katello-repos-latest.rpm # yum -y localinstall http://yum.theforeman.org/releases/1.16/el7/x86_64/foreman-release.rpm # yum -y localinstall https://yum.puppetlabs.com/puppetlabs-release-pc1-el-7.noarch.rpm # yum -y localinstall http://dl.fedoraproject.org/pub/epel/epel-release-latest-7.noarch.rpm # yum -y install foreman-release-scl python-django # yum -y update
Install Katello
Make sure that you have at least 8 GB of total RAM free before running the installer.
# yum -y install katello
Setup the Foreman Server
At this point the foreman-installer should be available to setup the server. Foreman can be installed without Katello, as Katello is now a plugin to Foreman (Katello was a standalone application in early days, not the case anymore).
# foreman-installer --list-scenarios
Available scenarios
Foreman Proxy (use: --scenario foreman-proxy-content)
Install a stand-alone Foreman Proxy.
Foreman (use: --scenario foreman)
Default installation of Foreman
Katello (use: --scenario katello)
Install Foreman with Katello
Foreman is the main part, as whole architecture is based on it. The rest is just integration to do certain tasks. To customise the installation, check a list of parameters available:
# foreman-installer --scenario katello --help
The answer file /etc/foreman-installer/scenarios.d/katello-answers.yaml can be used as well. We want TFTP and Puppet, but we don’t need DHCP and DNS as we already have infrastructure for this.
# foreman-installer \ --scenario "katello" \ --foreman-initial-organization "Lisenet" \ --foreman-initial-location "HomeLab" \ --foreman-proxy-dhcp "false" \ --foreman-proxy-dns "false" \ --foreman-proxy-tftp "true" \ --foreman-proxy-puppet "true" \ --foreman-proxy-puppetca "true" \ --foreman-puppetrun "true" \ --foreman-proxy-puppetrun-provider "ssh" \ --puppet-runinterval "3600"
In case we forget the admin password, we can use the following command to reset it:
# foreman-rake permissions:reset
This will reset the password of the default admin user to the one printed on the command line. After installation of Katello, we need to trust Katello’s CA certificate on our system (instructions for how to do that on a Linux OS, Chrome, Firefox etc can be found on the Internet). We will find katello-server-ca.crt in the /pub directory of the Katello server (in our case http://katello.hl.local/pub/katello-server-ca.crt).
Remove Katello
If required, Katello can be removed this way:
# katello-remove
Puppet Issues when /tmp is Mounted as noexec
This is something we learnt the hard way. In some cases, especially for RHEL 7 installations, if the /tmp directory is mounted as noexec, Puppet server may fail to run correctly, and we may see an error in the Puppet server logs similar to the following:
puppetserver[]: Failed to load feature test for posix: can't find user for 0
puppetserver[]: Cannot run on Microsoft Windows without the win32-process, win32-dir and win32-service gems: Win32API only supported on win32
puppetserver[]: Puppet::Error: Cannot determine basic system flavour
This is caused by the fact that JRuby contains some embedded files which need to be copied somewhere on the filesystem before they can be executed. To work around the issue, we can either mount the /tmp directory without noexec (not recommended), or we can choose a different directory to use as the temporary directory for the Puppet server process. For the latter option, we need to set the permissions of the directory to 1777.
# mkdir -m 1777 /opt/tmp
Open the file /etc/sysconfig/puppetserver for editing and change the following line specifying the tmpdir:
JAVA_ARGS="-Xms2G -Xmx2G -XX:MaxPermSize=256m -Djava.io.tmpdir=/opt/tmp"
Foreman Providers
Several Foreman packages are available to add functionality:
# yum search foreman-|grep "^foreman-.*support" foreman-assets.noarch : Foreman asset pipeline support foreman-console.noarch : Foreman console support foreman-ec2.noarch : Foreman Amazon Web Services (AWS) EC2 support foreman-gce.noarch : Foreman Google Compute Engine (GCE) support foreman-libvirt.noarch : Foreman libvirt support foreman-mysql2.noarch : Foreman mysql2 support foreman-openstack.noarch : Foreman OpenStack support foreman-ovirt.noarch : Foreman oVirt support foreman-plugin.noarch : Foreman plugin support foreman-postgresql.noarch : Foreman Postgresql support foreman-rackspace.noarch : Foreman Rackspace support foreman-sqlite.noarch : Foreman sqlite support foreman-vmware.noarch : Foreman VMware support
If we were to run on VMware, we would likely want to install the foreman-vmware package.
Upgrade Katello 3.5 to 3.6
Create a Backup
Take a snapshot of the virtual machine. Optionally, backup Katello:
# katello-backup /mnt/backup/ --features=all -y
Update the System
Install all available updates, if a new kernel is deployed, reboot the server.
# yum -y update
Repositories
Update the Foreman and Katello release packages:
# yum update -y http://fedorapeople.org/groups/katello/releases/yum/3.6/katello/el7/x86_64/katello-repos-latest.rpm # yum update -y http://yum.theforeman.org/releases/1.17/el7/x86_64/foreman-release.rpm # yum clean all && yum update -y foreman-release-scl
Update Packages and Run the Installer
# katello-service stop # yum -y update
# foreman-installer --scenario katello --upgrade

My installation keeps failing on ssl validation error. I will try again
Also, why you have disabled dhcp,tftp i.e. –foreman-proxy-dhcp=false –foreman-proxy-tftp=false
Don’t we need them for provisioning ?
You do need them for provisioning, yes. But I already had dedicated DNS/DHCP/NTP/FTP servers in my environment, and the plan was to use capsule with external services, so I set them to false during the installation.
Hi
Have you tried the above using Ansible in place of Puppet?
No, I never tried Katello with Ansible. My whole lab is based on Puppet, therefore never had a need for it I’m afraid.
Hi! Thanks for the excellent write up! I’ve been following along, building a full replacement for my old home lab that was built on spacewalk. Definitely looking forward to building out a new version with more config management and automation potential.
Out of curiosity, in the first parts for DNS/DHCP I noticed you were using iptables and ntp, but in this doc you switched to chrony and firewalld. Any particular reason for that, or just to move to the newer tools?
You’re welcome! This article was written back in 2016, chances are I was into firewalld/chrony at that time because I was studying for RHCE. The homelab series were written a couple of years later, when I switched back to iptables. While I can use both, I still prefer old good iptables over firewalld.