The benefit of having two Postfix servers relaying email to an external SMTP server is redundancy.
This article is part of the Homelab Project with KVM, Katello and Puppet series.
Homelab
We have two CentOS 7 (minimal) servers installed which we want to configure as follows:
admin1.hl.local (10.11.1.2) – will be configured as a Postfix relay
admin2.hl.local (10.11.1.3) – will be configured as a Postfix relay
Both servers have SELinux set to enforcing mode.
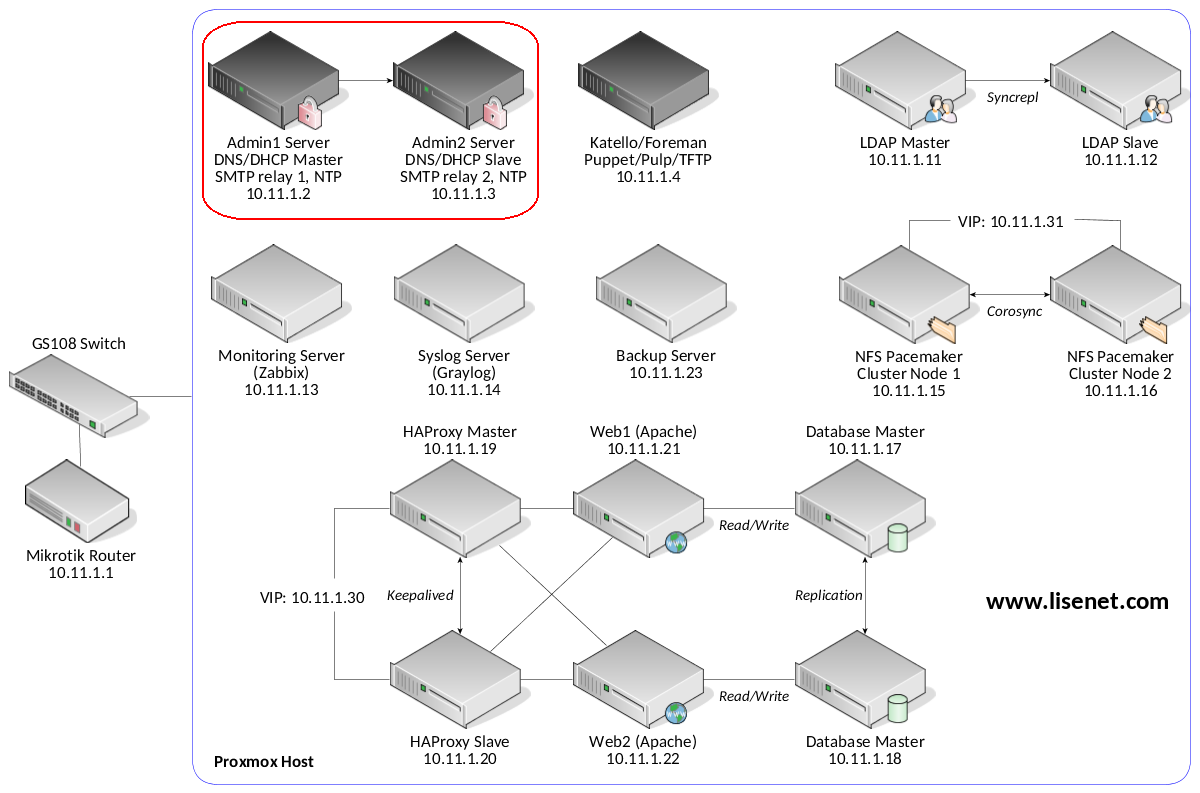
See the image below to identify the homelab part this article applies to.
Software
Software used in this article:
- CentOS 7
- Postfix 2.10
Install Postfix
Note that this section applies to both servers.
Install Postfix and ensure that the service is enabled:
# yum install postfix cyrus-sasl-plain # systemctl enable postfix
In case Sendmail is installed, remove it:
# yum remove -y sendmail*
Allow inbount firewall traffic:
# iptables -A INPUT -s 10.11.1.0/24 -p tcp -m state --state NEW --dport 25 -j ACCEPT
Configure Postfix Server as a Relay
Note that this section applies to both servers. Open /etc/postfix/main.cf for editing and configure the following:
smtpd_banner = $myhostname ESMTP inet_interfaces = all inet_protocols = ipv4 mynetworks = 127.0.0.0/8, 10.11.1.0/24 relayhost = [mail.example.com]:587 smtp_sasl_auth_enable = yes smtp_sasl_password_maps = hash:/etc/postfix/sasl_passwd smtp_sasl_security_options = noanonymous smtp_tls_CApath = /etc/ssl/certs smtp_use_tls = yes
Create a new file /etc/postfix/sasl_passwd and add the authentication details of the external SMTP server:
[mail.example.com]:587 [email protected]:passwd
Prevent non-root access:
# chmod 0600 /etc/postfix/sasl_passwd
Create a database file:
# postmap /etc/postfix/sasl_passwd
Check configuration and restart Postfix service:
# postfix check # systemctl restart postfix
Configure Postfix on a Null Client
When we configure other homelab servers to us Postfix to relay emails via admin1 and admin2, we can have a fallback relay defined (taken from the Postfix configuration file /etc/postfix/main.cf that’s on the Katello server):
relayhost = [admin1.hl.local] fallback_relay = [admin2.hl.local]
This gives us redundancy in a way so that if one of the SMTP relays is down, we can send emails out via the second one.
Here is an example taken from our Katello server when both relays are operational:
[katello]# echo test|mailx -s TEST [email protected]
Feb 18 18:09:52 katello postfix/pickup[23067]: 328C73D94: uid=0 from=<root> Feb 18 18:09:52 katello postfix/cleanup[23089]: 328C73D94: message-id=<[email protected]> Feb 18 18:09:52 katello postfix/qmgr[23068]: 328C73D94: from=<[email protected]>, size=421, nrcpt=1 (queue active) Feb 18 18:09:52 katello postfix/smtp[23091]: 328C73D94: to=<[email protected]>, relay=admin1.hl.local[10.11.1.2]:25, delay=0.13, delays=0.04/0.02/0.03/0.03, dsn=2.0.0, status=sent (250 2.0.0 Ok: queued as 4A557532) Feb 18 18:09:52 katello postfix/qmgr[23068]: 328C73D94: removed
We see that email was relayed via admin1. Now, if the admin1 server was down, the email would get relayed via admin2:
Feb 18 18:11:17 katello postfix/pickup[23067]: A81993D96: uid=0 from=<root> Feb 18 18:11:17 katello postfix/cleanup[23089]: A81993D96: message-id=<[email protected]> Feb 18 18:11:17 katello postfix/qmgr[23068]: A81993D96: from=<[email protected]>, size=421, nrcpt=1 (queue active) Feb 18 18:11:17 katello postfix/smtp[23091]: connect to admin1.hl.local[10.11.1.2]:25: Connection refused Feb 18 18:11:17 katello postfix/smtp[23091]: A81993D96: to=<[email protected]>, relay=admin2.hl.local[10.11.1.3]:25, delay=0.2, delays=0.01/0/0.08/0.11, dsn=2.0.0, status=sent (250 2.0.0 Ok: queued as C9F614D6) Feb 18 18:11:17 katello postfix/qmgr[23068]: A81993D96: removed

Hello,
First of all, thank you for this article. I was wondering if you can help me out with one problem though?
I have mada a cron.js file which is sending emails to the users, depending on server status. I have also configured postfix, as suggested here: sendgrid.com/docs/for-developers/sending-email/postfix/. When i execute file from
command line, for example node cron.js , everything works fine. But when i put that file in crontab, i get authorization error.
Do you know what the problem may be?
All the best
A couple of things you can check. Make sure that you use the same user to run the script, also use the full path to the executables. If these don’t help, the run the script in the debug mode. It might also be environment variables that aren’t the same when you run it from a CLI and via cron.
Hi,
I am not sure how many of the readers were successfully able to get the Postfix started sending emails…
I followed all the steps of the article. When I try sending test mail, I get following error in the /var/log/maillog
Jul 15 12:59:43 mumsrv-qe postfix/qmgr[4046]: A844F181C88: from=, size=456, nrcpt=1 (queue active)
Jul 15 12:59:45 mumsrv-qe postfix/smtp[7929]: warning: SASL authentication failure: GSSAPI Error: Unspecified GSS failure. Minor code may provide more information (No Kerberos credentials available)
Jul 15 12:59:45 mumsrv-qe postfix/smtp[7929]: A844F181C88: to=, relay=100.100.200.200[100.100.200.200]:587, delay=1176, delays=1174/0.02/1.8/0, dsn=4.7.0, status=deferred (SASL authentication failed; cannot authenticate to server 100.100.200.200[100.100.200.200]: generic failure)
IP has been modified for security reason.
It looks like your login credentials are incorrect.
Your article looks so good. However, I need a clarification regarding Email communication of Monitoring purpose. I have configured a relay Email Server (10.2.x.x) which connects to Main Email Server(192.168.x.x), both using same domain. I want around 10 users which was already configured in Main Email server to send Emails through 10.2.x.x. How do I achieve this ?
Example scenario:
User IDs in Main Email Server: [email protected], [email protected]
I want these two users only to send Email through relay Email server. Also I don’t want any other legitimate user of mydomain apart from above to be able to send Email through Relay Server.
However, If I give a user ID which was not created anywhere in my Main Email Server, this relay Email server is happily sending a email with this non-available user (Spam). How do I curtail this ?
regards,
M. Dinesh Ram
Hello,
Thank you for the idea.
I do not get why there is
relayhost = [mail.example.com]:587
in your relayhost’s configs. That would indicate that they are relaying all messages again and kind of bening there for nothing?
Relaying config with
relayhost =
would make more sense as general example?
– Aki
Hi Aki, the objective of the post is to configure Postfix to relay mail to an external SMTP server, in my case, the external SMTP server that I want emails relayed to before they get sent out to recipients is mail.example.com (not my real server DNS obviously). My SMTP server does SPAM filtering and applies custom blocklist rules. I hope this clarifies things.