Working with Katello – part 6. We will configure OpenSCAP plugin to receive automated vulnerability assessment and security compliance audits from Foreman hosts.
This article is part of the Homelab Project with KVM, Katello and Puppet series.
Homelab
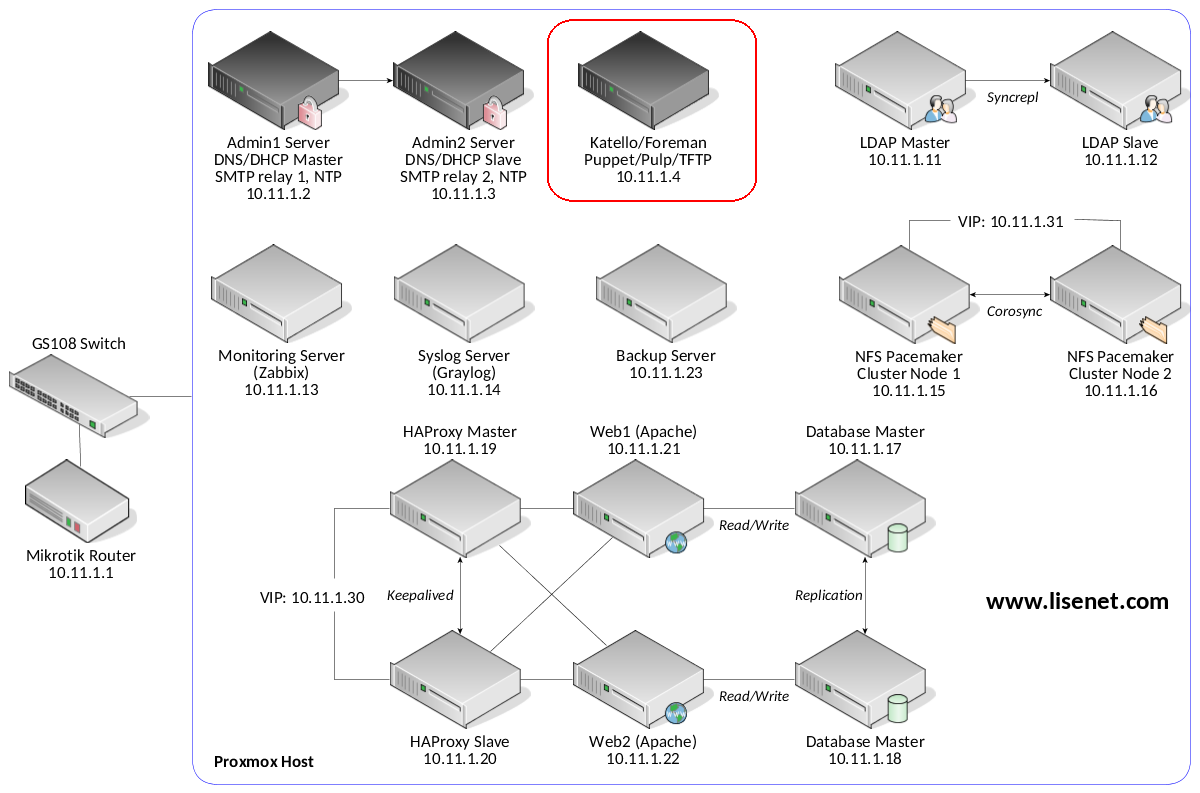
We have Katello installed on a CentOS 7 server:
katello.hl.local (10.11.1.4) – see here for installation instructions
See the image below to identify the homelab part this article applies to.
OpenSCAP
The Security Content Automation Protocol (SCAP) enables the definition of configuration and security policies, also the means of auditing for compliance with those policies. In Foreman, SCAP is implemented with the tools provided by the OpenSCAP project.
The OpenSCAP plugin enables Foreman to receive automated vulnerability assessment and security compliance audits from Foreman hosts. We can upload SCAP compliance contents, create compliance policies out of them and assign the policies to hosts or hostgroups.
Installation
Detailed installation instructions can be found on the Foreman website. See references for a weblink.
We need to install the following:
- Foreman OpenSCAP (foreman_openscap).
- Smart Proxy OpenSCAP (smart_proxy_openscap).
- foreman_scap_client.
- puppet-foreman_scap_client.
Install foreman_openscap
# foreman-installer --enable-foreman-plugin-openscap
Install smart_proxy_openscap
# foreman-installer --enable-foreman-proxy-plugin-openscap
If you want to, you can modify /etc/foreman-proxy/settings.d/openscap.yml with custom settings.
After installing smart_proxy_openscap on the proxy, refresh features of the proxy so it will register with OpenSCAP feature on the Foreman.
Install Puppet Module puppet-foreman_scap_client
This puppet module will automatically install foreman_scap_client and configure the client with all parameters needed for the operation of foreman_scap_client.
# puppet module install theforeman-foreman_scap_client --environment homelab Notice: Preparing to install into /etc/puppetlabs/code/environments/homelab/modules ... Notice: Downloading from https://forgeapi.puppet.com ... Notice: Installing -- do not interrupt ... /etc/puppetlabs/code/environments/homelab/modules └─┬ theforeman-foreman_scap_client (v0.3.18) └── puppetlabs-stdlib (v4.24.0)
After installing the module, import new Puppet classes via Katello WebUI:
Configure > Puppet Classes > Import environments from katello.hl.local
Setup Foreman Plugins Repository
Starting with puppet-foreman_scap_client 0.3.14 shipped with Foreman 1.14 the Foreman plugins yum repo can be set up if you define at least Foreman’s major release version. This repository is needed to install foreman_scap_client, which will fail otherwise.
Note that packages are not signed.
Create a new repository and sync it:
# hammer repository create \ --product "el7_repos" \ --name "foreman-plugins-117" \ --label "foreman-plugins-117" \ --content-type "yum" \ --download-policy "on_demand" \ --url "https://yum.theforeman.org/plugins/1.17/el7/x86_64/"
# hammer repository synchronize \ --name "foreman-plugins-117" \ --product "el7_repos"
Add the new repository to the content view:
# hammer content-view add-repository \ --name "el7_content" \ --product "el7_repos" \ --repository "foreman-plugins-117"
Publish a new version of the content view that includes the Foreman plugins repository:
# hammer content-view publish \ --name "el7_content" \ --description "Publishing foreman plugins 1.17"
Let us see the version number that we want to promote:
# hammer content-view version list
Promote content view version to our “stable” lifecycle environment:
# hammer content-view version promote \ --content-view "el7_content" \ --version "11.0" \ --to-lifecycle-environment "stable" \ --description "Publishing foreman plugins 1.17"
At this point the new repository should be available to clients.
Usage
Create Default SCAP Content
This following will search for scap-security-guide SCAP contents and create SCAP content on the Foreman.
# foreman-rake foreman_openscap:bulk_upload:default Saved /usr/share/xml/scap/ssg/content/ssg-centos6-ds.xml as Red Hat centos6 default content Saved /usr/share/xml/scap/ssg/content/ssg-centos7-ds.xml as Red Hat centos7 default content Saved /usr/share/xml/scap/ssg/content/ssg-firefox-ds.xml as Red Hat firefox default content Saved /usr/share/xml/scap/ssg/content/ssg-jre-ds.xml as Red Hat jre default content Saved /usr/share/xml/scap/ssg/content/ssg-rhel6-ds.xml as Red Hat rhel6 default content Saved /usr/share/xml/scap/ssg/content/ssg-rhel7-ds.xml as Red Hat rhel7 default content
Create Policy Wizard
Open Katello WebUI and navigate to the following:
Hosts > Compliance > Policies > New Compliance Policy
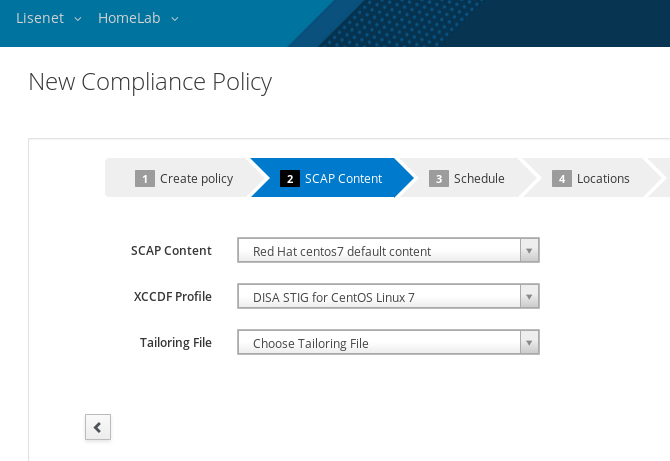
Create a new policy and provide the following details:
- Name of the policy (e.g. homelab).
- Choose which SCAP content and SCAP profile to apply (e.g. STIG).
- Choose schedule when to run this policy (e.g. weekly on Sundays).
- Select which location / organization thes policy belongs to (e.g. Lisenet / HomeLab).
- Choose which hostgroups you wish to pply this policy to (e.g. el7_group).
The result should look something like this:
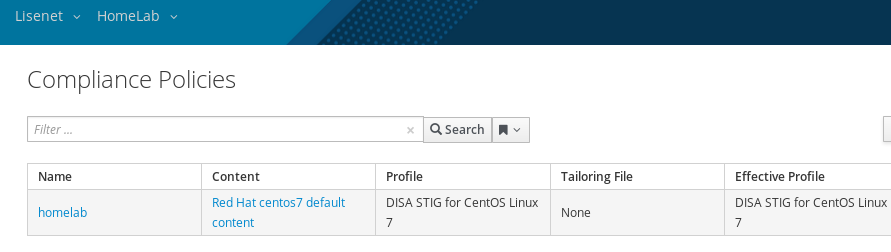
This will assign the policy to the specified hostgroup. All hosts which belong to the hostgroup will automatically be assigned to the policy, and the Puppet class will be included.
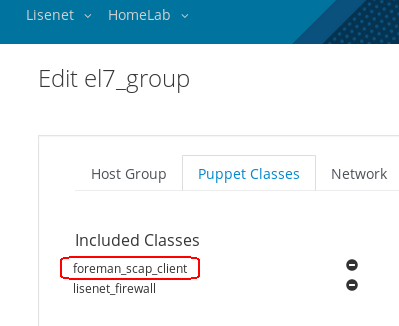
Open Katello WebUI, edit Host Group and specify OpenSCAP Proxy:
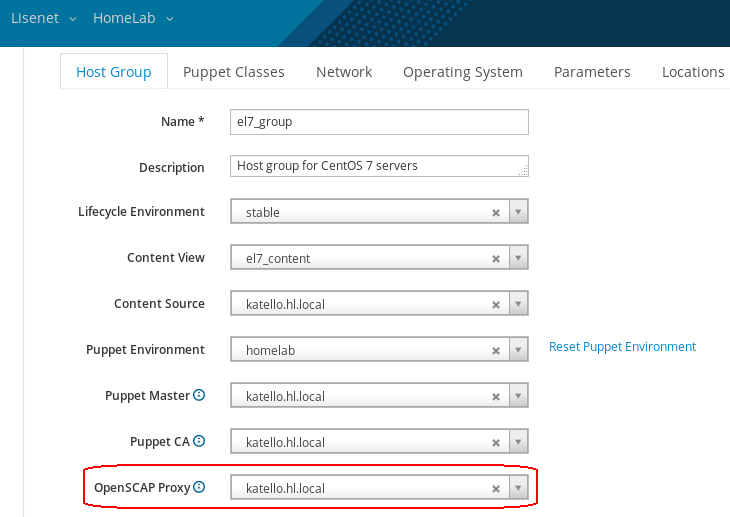
Make sure that all hosts that are assigned to the hostgroup have OpenSCAP Proxy assigned.
Hosts will get foreman_scap_client automatically installed and configured on the next Puppet agent run. There will be a cron file created /etc/cron.d/foreman_scap_client_cron that runs according to the schedule that was chosen when creating the policy.
How to Run foreman_scap_client Manually
Check the content of the cron file on a host you want to run the client on (we use db1.hl.local):
[db1]# cat /etc/cron.d/foreman_scap_client_cron # DO NOT EDIT THIS FILE MANUALLY # IT IS MANAGED BY PUPPET # foreman_scap_client cron job # Runs foreman_scap_client 1 0 1 * * 0 root /usr/bin/foreman_scap_client 1 > /dev/null
Copy the line from the file and run:
[db1]# /usr/bin/foreman_scap_client 1 [...] Uploading results to https://katello.hl.local:9090/compliance/arf/1
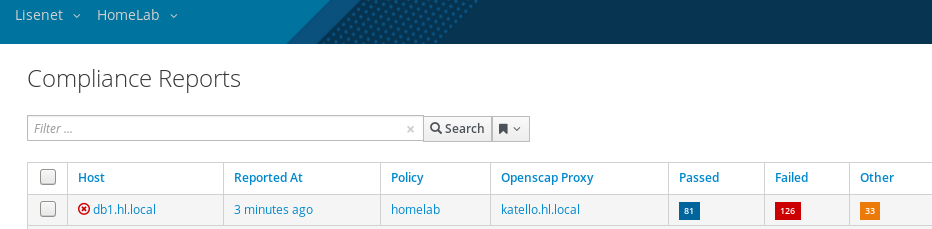
Reports can be found here: Hosts > Compliance > Reports
SCAP Workbench and Tailoring Files
Default SCAP policies may not suit your needs and can therefore be edited. SCAP Workbench is a graphical utility that offers an easy way of doing that.
Workbench allows you to modify an XCCDF profile in an easy way without changing the respective XCCDF file. The tool provides a graphical way to enable or disable XCCDF elements. Your changes can be stored as an XCCDF tailoring file.
References
https://www.theforeman.org/plugins/foreman_openscap/0.8/index.html
